Thread #108607681
File: 6yB9mG7iAP.png (379.5 KB)
379.5 KB PNG
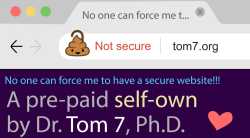
guys, we should ditch https because its toxic max-security, we shouldnt have the bare minimum of security, its hurting our real internet experience of a popup warning because how there are third world bug people who constantly engage being bad actors to every normal person on the internet but we will NEVER talk about that. should we ditch https for some homemade security layers?
45 RepliesView Thread
>>
>>
>>
>>
>>
File: 1770445082361151.jpg (26.3 KB)

26.3 KB JPG
>i-if sites don't have https everyone will be able to see the sites you visit!!!
The site is a personal blog, I don't care if anyone else sees that I'm visiting it, maybe whoever is eavesdropping my connection might find it interesting it too.
I would, however, like to have encryption when I'm sending messages to my contacts, because nobody needs to read my private conversations.
>NOOOOOOO actually privacy is le bad! i-if you have nothing to hide you have nothing to fear!!
>>
File: 1774566508548234.gif (1.9 MB)

1.9 MB GIF
>>108607681
>bare minimum of security requires 7 billion lines of code and 3 phds to implement from scratch
>>
>>108608605
Its not just about encryption. Without HTTPS you have no way of knowing if the data you're receiving is from the website you're trying to access or if its been intercepted and replaced with something malicious.
>>
>>
>>108607752
the video op neglected to link to explains it in great detail
https://youtu.be/M1si1y5lvkk
>>
>>
>>
>>
>>
>>108609630
>tldr boomer is too stupid to install certbot or move his domain to cloudflare
if you believe this then i don't believe you watched the video, because for one that's not at all the point of the video, and also what he did instead was a deliberate "fuck you" to browsers like chrome putting up warnings for any site not using https and his solution is far, FAR, more difficult than just folding and setting up certbot/cloudflare
>>
>>
>>108609672
the video is complaining about just that. that his personal website that has been there since the '90s that doesn't handle anything private at all is now causing big scary warnings in modern browsers simply because it's not https. so he goes full malicious compliance by rolling his own https proxy encryption handling that is as deliberately hilariously insecure as possible. if you've seen any of his previous videos you know it's gonna be gud
>>
>>108609630
>boomer is too stupid to install certbot or move his domain to cloudflare
he says about a guy who wrote a 25-page paper for SIGBOVIK about the subject and how he practically worked around having a secure website while having a "secure website".
i bet you feel so intelligent for just doing what google asks you to do as they intend you to do it.
>>
>>
File: (((you))).png (267.8 KB)

267.8 KB PNG
>>108609630
>tldr boomer is too stupid to install certbot or move his domain to cloudflare
>>
>>
>>108609630
His publication history makes it obvious he's not stupid. And while he holds a minority position it's not exactly fringe or extremist. If anything it's on the rise among everyone who doesn't operate their own peering/surveillance networks. It's actually illegal in all 5 eyes countries to blanket weiretap unencrypted traffic, it's only legal for encrypted traffic. Think about it.
>>
>>
>>
File: wait-a-sec-v0-3iihdr67ktfc1-1224861962.jpg (38.8 KB)

38.8 KB JPG
>>108611149
>It's actually illegal in all 5 eyes countries to blanket weiretap unencrypted traffic, it's only legal for encrypted traffic. Think about it.
suddenly things make more sense
>>
>>108611803
yes, he did
https://sourceforge.net/p/tom7misc/svn/HEAD/tree/trunk/httpv/
>>
>>
>>
File: 1770359432090275.gif (905.5 KB)

905.5 KB GIF
>>108609630
>cloudflare
>these random hiccups since 2024
>used to be actually 99% uptime
>>
>>
>>108607681
>should we ditch https
No.
>for some homemade security layers?
Especially no. That's only going to make it worse. Security through obscurity is no real security at all.
However, we probably should ditch the "use https for everything" approach we're using today. Do I care if my ISP, the government, or anyone else watching my connection can see that I read a web page about the history of light bulbs or whatever else? Do they care that I did? No. Then why secure that with https? But definitely still use it for anything that's handling a password, card number, bank details, etc.
>>
>>
>>
>>
>>
>>108612223
but youre not only reading about light bulbs
because the light bulb web page wants to make money, they'll have ads
and those ads will track you to "optimize your experience" aka manipulate you. they will (they did) build a profile for you, so they can show you ads that you are more likely to click.
and now viewing that light bulb web page not only tells everyone en route that youre interested in light bulbs, but also your ad profile via the content of the ads. youre getting ads for dragon dildos, extra small condoms and diapers for a reason. every time you open an unencrypted page with ads. your ad profile alone is worth encrypting all traffic.
>hurr i have an adblocker
>>
>>
>>
>>
>>
>>108614182
https://en.wikipedia.org/wiki/Parallel_construction
>>
>>
>>
>>108607752
HTTPS (Hypertext Transfer Protocol Secure) encrypts data between a web browser and server using Transport Layer Security (TLS). It ensures data integrity, confidentiality, and authentication via a "handshake" process, where a server presents a certificate, and a secure session key is exchanged, securing communication from eavesdropping.
>>
>>
Started watching the video to see how far I'll get before getting angry, but was pleasantly surprised. It's actually a cool way to serve just-my-prose websites because hotel routers and american ISP middleboxes will see TLS handshake and fuck off.