Thread #108274355
File: 1764124372103818.png (24.7 KB)
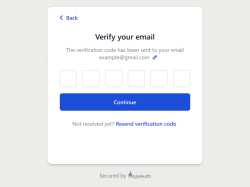
24.7 KB PNG
1980-2025
>if you reuse passwords on different websites you're a retard begging to get pwned
2025-
>your gmail password is the key to your entire fucking life
Make it make sense
48 RepliesView Thread
>>
>>
>>
>>
>>
>>108274801
I don't see how they will be more secure, and they'll just lead to people getting locked out if they become the only authentication method and the passkey dies with the original device. Hackers will also find ways to extract the passkeys out of the TPM or android equivalent and use them... hopefully they're revocable.
>>
>>
>>
>>108274355
>your gmail password is the key to your entire fucking life
Is now the time to tell you I have no idea what that is?
My life has featured zero impact.
>Make it make sense
I'm struggling anon, I really am. At what point do you imagine gmail to be mandatory for use?
>>108274366
>Thats why Google is pushing passkeys and 2fas now. And soon, digital ids
You honestly think they're incapable of tracking you through your metadata and habits, after giving them these for over a decade n ½ to feed into their abusive algorithyms?
That's pure to stop other people using your shit with the crappy security policies users insist on deploying.
>>
>>108274801
>more safe than a strong password
Passwords fail. Regular. Like f'kin clockwork. Botnets of the hundreds of thousands are attempting anything they can find.
Fuck all this "passkeys" bollocks and other cuck options being generated.
There have existed secure mechanisms to achieve this for decades. Plural. You use them daily, frictionlessly. You're using one *right now*.
x.509
x.509 keys to the encrypted transport for like 99% of web traffic. It's good enough for your docile media. It's good enough for your bank. It's good enough for your .gov.
It's battle tested. A proper implimentation is yet to be fucked over.
You may be thinkin': But anon, that's websites.
And? It's public key cryptography. It works just as well for authorisation and authentication too.
SSH is pretty much the standard for remote server admistration. I can dial into my servers and they don't bother challenging me.
I'm just logged in.
The "how" is I put my public key½ up there, and it's expecting key login.
My private key can solve the cryptographic challenge, and only my private key can solve the cryptographic challenge. I'm afforded security - providing I can keep the physical security of the private key secure - and convenience...
This isn't 'new' technology. It's been a standard for a decade (almost) and it's failed - on a global scale - precisely zero times(not involving key leaks).
How many times have passwords failed in the last year?
2? 5? 10?
>>108274828
Um. Use something else?
>I have hundreds of websites where the account is linked to my gmail.
How many o them would actually be problematic is google recinded your access?
Change them first.
>>108274855
>1995
>Linux is going to be good and stable in 10 years
Well. It ran from Dec 2000 -> Sept 2019... Sounds stable to me.
Until I rebooted for a kernel change, one of my servers had in excess of 1500 days uptime...
>Linus is going to be good and stable in 10 years
He's not stable now?
>>
>>108274355
yeah and google use to tell people not to put anything on the internet that can identify their real life identity. and now google encourages people to reveal their true identity to the entire planet.
google will do anything, at the moment, they believe will generate money for them. they want your entire life in one google account, because it makes them money. just like they want you to reveal yourself to everyone, because they can harvest your data and generate revenue off of it.
>>
>2017
>weve made totp and authentication apps which offer superior security to sms/phone calls and will function as a replacement.
>2026
>having trouble finding the totp code? It's ok, click here to use SMS instead to the number you were forced to add to your account still
I want to fucking die
>>
>>
>>
>>
File: KeePass_Logo_(2016).svg.png (82.3 KB)

82.3 KB PNG
>>108274355
My bigger problem is pic related.
>need to reopen database virtually every time I use it (because I don't log into shit every 5 minutes)
>constantly one keylogging incident away from getting pwnd from here to mars when opening the database
>typing long database password is huge a pain in the ass on my desktop PC and windoze/lunix laptop anyway
>but on phone and macbook with biometrics enabled for the database I can be forced by feds to give it up if it ever comes to that (have no reason to, but I don't like the possibility)
>last but not least, always going that my database is not being stolen by mitm when getting syncthing'd between my devices
Is there really no better way?
>>
>>
>>
>>108274366
Digital IDs are pushed by government retards who know nothing about security, companies hate dealing with real IDs because eventually they will get a data breach and be held liable for the data stolen, they two outcomes are either paying a huge fine or go bankrupt.
>>108274801
Much higher bits of entropy. Even a strong password is weak compared to passkeys.
There is no transmission of secrets, they are phishing resistant, theyare immune to credential stuffing, they remove the weakest link in password security (the user), and they cannot be brute forced.
Passkeys are just SSH keys for normies.
The only weakpoint of passkeys is that if you lose your device or it gets stolen (and passkeys are not synced over the internet) then you are locked out of all the accounts that do not have other recovery methods.
>>108274828
One website/app at a time, manually.
>>
>>
>>
>>
>>
>>
>>
>>108275643
> let me use my fucking password
Then just do so?
I’ve never seen one of those (or >use your Apple ID >use Amazon account ones) where making a “traditional” account is just one or two (somewhat dark-patterned, I’ll admit) clicks away.
>>
>>
>>108275732
But that’s different from using Gmail for everything.
And yes, I’ve encountered those, but only for some (actually quite huge in my country) shop, where I don’t see too much risk, but yea, it’s very odd that
>just give us an email address
>yoooo, you’ve got an account now!
Apparently is a sane practice.
Don’t really care for some shopping website but I would t use this for anything important.
>>
>>108275032
i used to just receive everything by SMS or email cuz I didn't want to install some shitty authenticator app, until I had to use a service that only supported auth apps. Set up pass-otp which is actually so much better and now i can generate codes on my laptop instead of having to check my phone every time
>>108275129
>set cache duration to 1h instead
>if worried about keylogger, just change 1 master password instead of 100 slave passwords
>use short password if you like, if you need to change it it's only 1 password
>biometrics LMAO
>database should be encrypted at rest so it doesn't really matter if someone else gets a copy
The nice thing is, if you think someone has gotten in to your passdb, you already have a list of services whose password you need to change. no forgetting.
plus it's not like remembering your passwords manually solves any of these issues
>>
>>
>>108275032
>I want to fucking die
Easily arranged.
>>108275129
>Is there really no better way?
X.509?
But as most places neglect to offer that as on option. Not really.
Unless of you meant locking keypass using a file and not a password.
>>108275388
>eventually they will get a data breach and be held liable for the data stolen,
Valide concern.
Are you able to evidence there will actually be some form on consquences to said breach? Seems to happen all the time and there doesn't appear much done...
>>108275732
>started switching to email code verification
Still a security fail in the transmission of the code. Then consider most providers compromised and autonomous response isn't beyond plausible.
Shouldn't *need* transmitting. That's a massive implimentation fail.
>Consider yourself lucky if you have never encountered that.
If I encountered that I would 180° for the theater peddled as security. You stick around you deserve what happens next.
>>108275797
>i used to just receive everything by SMS
Hmm. I know. I'll transmit this code in plain text. Across a network that allows for spoofing and provisions zero authentication. A network that features assured intercept.
Sounds safe.
>now i can generate codes on my laptop instead of having to check my phone every time
Convenience and security. Features of a good implimentation...
>>
>>108275129
literally me
yeah if my keepass password ever gets found out I am literally BEYOND fucked, everything is in there
>but on phone and macbook with biometrics enabled for the database I can be forced by feds to give it up if it ever comes to that (have no reason to, but I don't like the possibility)]
oh
i actually never thought about that before. Not just the feds but any random person can force you to open it on your phone... Damn pretty bad. I guess I really should stop using biometrics, but it makes it so much easier than typing the whole long thing in...
>last but not least, always going that my database is not being stolen by mitm when getting syncthing'd between my devices
well even if they get it they cant do anything without the password
>>108275032
>>108275797
I was against topt when i thought it required you to have google or other authenticator app on your phone. Since I realized that keepass can do it, I've been in favor of them.
>>
File: security.png (25.7 KB)

25.7 KB PNG
>>108276437
>I guess I really should stop using biometrics, but it makes it so much easier than typing the whole long thing in...
How valuable is that convenience if the easiest path for an attacker is to start cutting pieces of you off?
Lets pretend they have some concern for your safety and well being. This data is being placed into the public domain constantly - when you inevitably lose control over this, how to you intend to rotate this to something you do control. Changing fingerprints, faces, eyes, etc isn't that convenient for most.
As for passwords... Picrel.
>>
>>
File: 5bc-418422764.png (36.4 KB)

36.4 KB PNG
>>108275142
>(((Certain people))) don't like men with high testosterone so they spend trillions of propaganda telling people smoking, which increases testosterone, is le bad and problematic
>>
>>108276198
>Are you able to evidence there will actually be some form on consquences to said breach?
The consequences are identity theft and being a target for scams. It happened to my uncle, it was not fun for him, he was investigated by the police and had to issue new identity documents and new debit cards.
>>
>>108276531
I was meaning more consequences for those unable to secure the data, than consequences for the victims.
Hence my previous statement regarding the regular breaches and no tangible conseuqences. If I had meant the victims, lists of conseuqences can be applied.
>>
>>108276546
https://commission.europa.eu/law/law-topic/data-protection/rules-busin ess-and-organisations/enforcement-a nd-sanctions/sanctions/what-if-my-c ompanyorganisation-fails-comply-dat a-protection-rules_en
https://commission.europa.eu/law/law-topic/data-protection/rules-busin ess-and-organisations/enforcement-a nd-sanctions/sanctions/can-my-compa nymy-organisation-be-liable-damages _en
In the EU, GDPR sanctions are up to 20 million € or 4 % of the business' total annual worldwide turnover, which one is greater.
>>
>>
>>108277044
Don't know about that but here's a list of fines:
https://en.wikipedia.org/wiki/GDPR_fines_and_notices
Just CTRL + F "secur" to find all the data security related fines.
>>
>>108277199
I note between 2021 and 2024 there is five incidents listed. I'm pretty sure there was more than five data breaches that impacted eurpeans.
Pretty sure a year averages more than five.
Sure, that list may be incomplete. But it's not adding much support to your premise that a mass data loss features consequences, and even less to support that companies pushing the responsibilty to government for retaining the data securely will feature consequences on loss.
>>
>>
>>108277274
You don't have to know the passkey to use it, it can be on your phone or on a physical key. Therefore it is less vulnerable to bad passwords and everything implied by having your average techlet securitylet normie choose a password. I guess it can also prevent >>108276481 picrel
>>
>>
>>
>>
>>
having 1 highly secure 2fa or hypothetically even more factor thing thing you maintain a session for makes way more sense than having a bunch of accounts on random websites.
It doesn't have to be google but if someone doesn't have some kind of sso thing on their site I will often just not use it, sorry your garbage website is not worth me making a login for.
Also just use burner gmail accounts i have several